Secure Your Internet-Facing Infrastructure
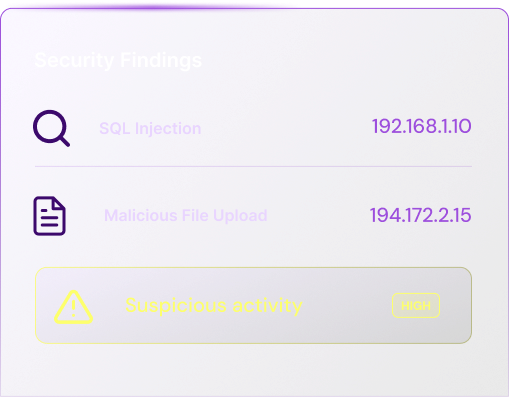
Our external penetration testing evaluates your internet-facing infrastructure to identify publicly exploitable vulnerabilities before adversaries do. While automated scans can detect open ports and outdated services, our approach goes further — validating exposure, identifying misconfigurations, and simulating real-world attack paths against externally accessible systems.
We assess the true risk of exposed services, confirm exploitability through controlled techniques, and prioritize findings based on potential business impact.
Our Engagement Process
Every engagement follows a structured methodology designed to ensure clarity, technical depth, and measurable risk reduction — from initial scoping to validated remediation.
Scoping & Planning
We begin by defining the scope, attack surface, and engagement objectives. Access levels, environments, timelines, and reporting expectations are aligned to ensure clarity before testing begins.

Penetration Testing
In this stage, our certified offensive security professionals simulate realistic attack scenarios across the agreed scope. Findings are validated for exploitability and contextualized based on real-world risk.
.svg)
Reporting & Retest Validation
You receive structured, prioritized findings with clear remediation guidance. Once fixes are implemented, we can conduct a formal retest to validate remediation and strengthen assurance.
Do not wait for a breach to discover your weaknesses.
Stay ahead of real-world threats
Retest Assessment
An optional retest verifies that identified vulnerabilities have been correctly remediated and are no longer exploitable, with a digitally signed verification certificate issued upon successful completion.